Managed Data Backup
Expert data protection, backup, and compliance solutions designed to reduce risk, safeguard critical information, and ensure rapid recovery when the unexpected happens.
Safeguard against unexpected data loss
Unexpected data loss whether from hardware failures, accidental deletions, ransomware, or cyber-attacks can disrupt operations and expose your business to significant financial and reputational risk. When data disasters strike, backups alone are not enough. True resilience requires a structured business continuity strategy that protects data continuously and restores operations quickly under pressure. Without a comprehensive resilience framework, organizations face:
- Operational downtime
- Financial and reputational damage
- Compliance exposure
- Permanent loss of critical business data
Comprehensive data protection framework
True resilience is built on layered controls that protect, isolate, validate, and recover data under any condition.
Automated Incremental Backups
Protect every change, every day
Our automated incremental backup architecture continuously captures data changes, ensuring minimal data loss exposure and precise recovery capability.
Rather than re-copying entire systems, incremental protection records only what changes. This reduces storage overhead, shortens backup windows, and minimizes performance impact on production systems.
Key capabilities include:
- Continuous automated backup with minimal system impact
- Frequent capture of data changes
- Reliable point-in-time recovery
- Short backup windows and optimized storage efficiency
This ensures data integrity, accuracy, and rapid restoration when incidents occur.
Fast Setup, Search, and Recovery
Protection that starts immediately
Data protection should not require weeks of configuration. Our platform is engineered for rapid onboarding and operational simplicity.
Organizations can deploy protection in under 30 minutes, with automatic discovery of systems and workloads. Streamlined search and restoration workflows allow teams to quickly locate and recover critical data without complex procedures.
Fast setup ensures protection begins immediately. Efficient recovery ensures business operations resume without unnecessary delay.
Unified Data Protection
One platform. Complete visibility.
Fragmented legacy backup systems create administrative overhead and inconsistent protection policies.
Our unified protection framework centralizes management across cloud and on-premises environments, delivering consistent policies, consolidated reporting, and simplified administration.
This approach provides:
- Centralized management across all workloads
- Seamless replacement of legacy backup solutions
- Consistent enforcement of protection policies
- An intuitive interface that supports IT teams at all levels
Unified protection reduces complexity while increasing control.
Immutable Backups
Tamper-proof recovery you can trust
Immutable backups ensure that once data is written, it cannot be modified, encrypted, or deleted during its retention period even by privileged users.
This creates guaranteed clean recovery points during ransomware incidents or insider threats.
Immutability provides:
- Tamper-proof protection
- Ransomware-resistant backup states
- Guaranteed recovery integrity
- Compliance-aligned retention enforcement
Technologies may include Write-Once, Read-Many (WORM) storage, locked object storage policies, and hardened backup repositories.
Even in severe compromise scenarios, trusted recovery data remains intact.
Air-Gapped Backup Isolation
Preventing access before damage occurs
Air-gapped backups isolate backup systems from production networks, reducing the risk of malware spreading into backup repositories.
While immutability prevents data alteration, air-gapping prevents unauthorized access in the first place.
Air-gapped strategies:
- Separate backup storage from production systems
- Block automated lateral movement attacks
- Require authenticated, deliberate recovery access
Together, immutability and isolation create layered ransomware defense.
Automated, Policy-Driven Backup Management
Consistency without manual oversight
Effective resilience is governed by centralized policy and not manual execution.
Protection policies define what data is protected, how frequently backups run, how long data is retained, and which security controls are enforced.
Policy-driven automation ensures:
- Consistent protection across all workloads
- Reduced human error
- Automatic enforcement of security standards
- Alignment with regulatory and compliance mandates
As environments evolve, protection remains consistent.
Data Recovery & Business Continuity
Designed for real-world incidents
When downtime is not an option, recovery speed and precision are critical.
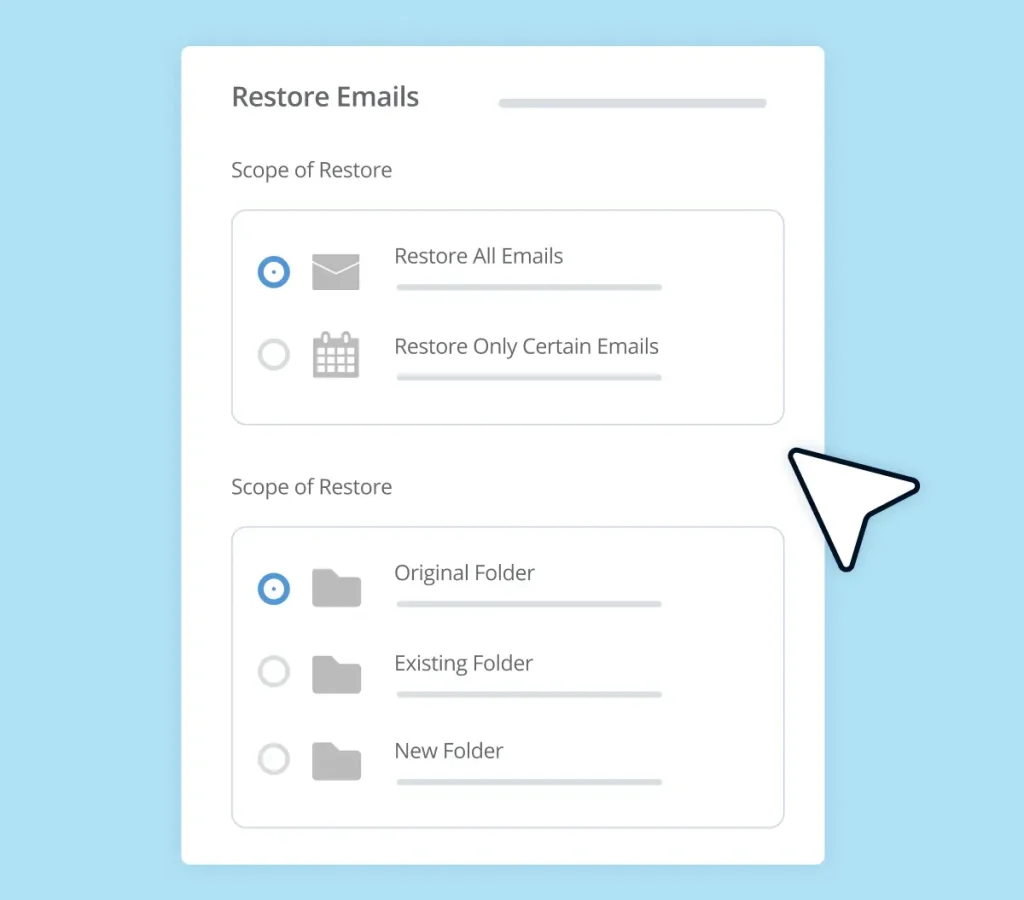
Modern recovery capabilities support both granular and full-scale restoration.
Granular recovery enables restoration of individual files, emails, and application components without disrupting entire systems.
Full-scale recovery enables restoration of entire workloads or environments when widespread impact occurs.
Point-in-time recovery allows data restoration to a known-good state prior to compromise.
Regular recovery validation and testing ensure restoration processes are reliable, repeatable, and ready under pressure.
Business continuity is not theoretical, it must be proven.
Data Security Controls
Protection across the entire data lifecycle
Data protection extends beyond backup creation. Both active and stored data must remain secure.
- Security controls include:
- Encryption in transit and at rest
- Role-based access enforcement
- Least-privilege user controls
- Protection against credential misuse
- When combined with immutability and isolation, these controls ensure backup data remains accurate, complete, and trustworthy.
Data Intelligence & Visibility
Governance through insight
Resilience requires visibility.
Data intelligence provides real-time monitoring of backup success rates, workload protection coverage, retention usage, and storage growth trends.
Structured reporting supports audit readiness, regulatory compliance, and executive decision-making.
Proactive visibility replaces reactive troubleshooting.
Data Portability
Long-term flexibility without lock-in
Data portability ensures that protected data remains accessible and transferable across environments.
Organizations can restore workloads to alternate sites, secondary clouds, or temporary recovery locations. Portability supports migrations, infrastructure changes, and regulatory data residency requirements.
Vendor lock-in is reduced. Long-term adaptability is preserved.
Why Managed?
Backup software alone does not guarantee resilience.
Tools do not validate recovery readiness. They do not continuously monitor protection gaps. They do not enforce immutability correctly. They do not align strategies with compliance mandates.
A managed, structured approach ensures resilience is operational, not theoretical.
Toos Solutions continuously monitors, validates, tests, and optimizes your resilience strategy to ensure protection performs when it matters most.
Our Approach
We implement resilience as a structured lifecycle:
1. Assess & Design
Evaluate workloads, risk exposure, and regulatory requirements.
2. Deploy & Configure
Implement incremental, immutable, unified, and isolated protection strategies.
3. Automate & Monitor
Enforce policy-driven protection across all environments.
4. Validate & Test
Confirm recovery reliability through structured validation exercises
5. Report & Optimize
Deliver executive visibility and continuous improvement. Resilience must be engineered, not assumed.


Business Impact
Our unified resilience strategy:
- Minimizes operational downtime
- Protects against ransomware-driven data destruction
- Reduces administrative complexity
- Replaces fragmented legacy systems
- Strengthens regulatory compliance
- Enables rapid, confident recovery
By combining incremental protection, unified management, immutability, isolation, intelligent monitoring, and validated recovery, organizations remain secure, compliant, and operational.
Ready to strengthen your data resilience?
Data loss is not a matter of if, it is a matter of when. Ensure your organization is prepared with structured, secure, and validated data protection that performs under real-world pressure.
Start with a resilience assessment and gain a clear, actionable roadmap to stronger backup security, faster recovery, and continuous operational protection.


