Reduce Risk.
Ensure Compliance.
Stay Resilient.
Proactive Vulnerability Management
In today’s interconnected digital environment, unmanaged vulnerabilities create real business risk.
Proactive vulnerability management helps organizations:
- Identify security weaknesses before attackers exploit them
- Reduce the risk of service disruption, data loss, and financial impact
- Prioritize remediation based on real‑world risk, not raw scan data
- Support regulatory and audit requirements
- Maintain operational resilience across evolving IT environments
By taking a continuous, risk‑driven approach, organizations gain clear visibility into their exposure and can focus remediation efforts where they matter most.

What True Vulnerability Management Looks Like
A one-time scan is not security.
A spreadsheet of vulnerabilities is not protection.
True vulnerability management requires continuous visibility, intelligent prioritization, structured remediation, executive accountability, and measurable outcomes.
That is what we deliver.
Continuous Scanning & Real-Time Exposure Detection
We provide ongoing automated assessments across endpoints, servers, networks, cloud environments, hybrid infrastructure, and IoT or edge devices.
Unlike traditional periodic scans, our 24/7 monitoring identifies new exposures as they emerge, drastically reducing exposure windows and limiting attacker opportunity.
You gain continuous awareness of your attack surface and not just quarterly snapshots.
Risk-Based Prioritization That Protects What Matters Most
Not every vulnerability requires immediate action.
We analyze findings through the lens of real-world exploit activity, active threat intelligence, asset criticality, business impact, and operational dependency.
This ensures your team focuses on vulnerabilities that could genuinely disrupt operations rather than low-risk technical noise.
Security resources are finite.
We ensure they are applied where they matter most.
Decisive Remediation & Verified Resolution
Detection without action creates false confidence.
We provide clear remediation guidance, patch coordination support, configuration hardening plans, compensating control recommendations, and structured tracking through to resolution.
Our approach ensures vulnerabilities are not just identified but resolved, verified, and documented.
Every critical issue is tracked.
Every remediation is confirmed.
Every exposure window is reduced.
Executive Visibility & Board-Ready Reporting
Cybersecurity is now a leadership responsibility.
We deliver structured executive reporting that includes quantifiable risk metrics, remediation timelines, exposure trend analysis, compliance alignment tracking, and program maturity indicators.
This transforms vulnerability management into an executive assurance function and not merely a technical activity.
Your board does not need raw vulnerability data.
They need risk clarity.
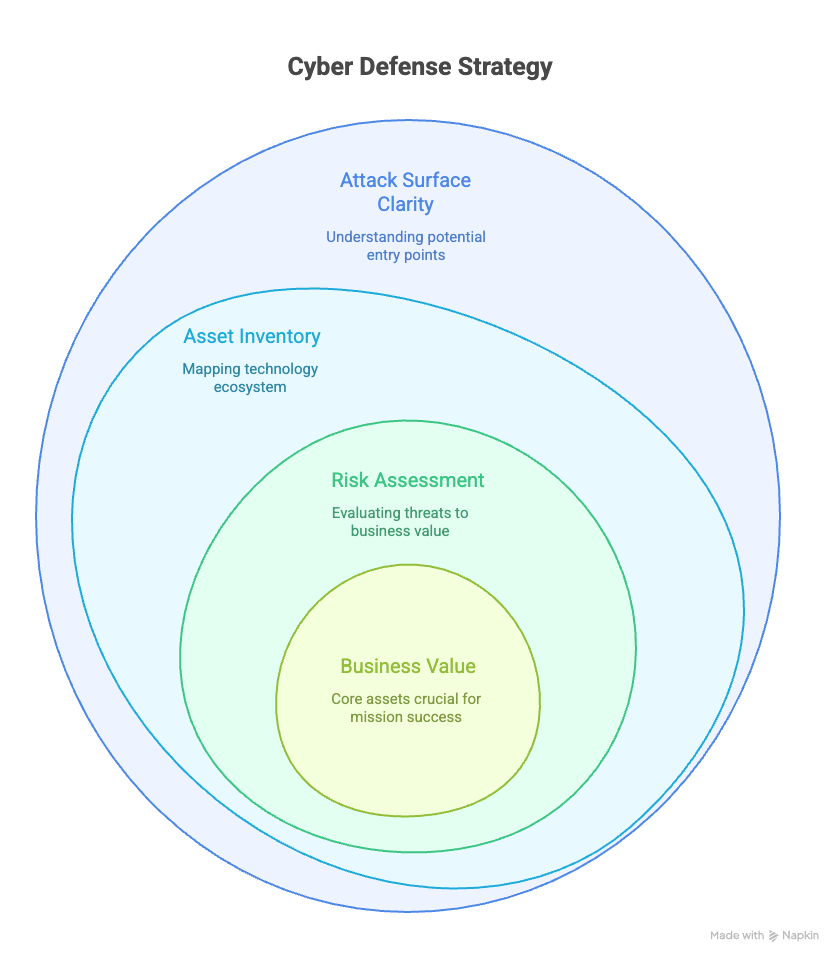
Total Attack Surface Visibility
You cannot protect what you cannot see.
We establish comprehensive asset discovery across on-prem infrastructure, cloud platforms, remote endpoints, SaaS environments, and operational technologies. Each technical asset is mapped to business value, ensuring security priorities align directly with mission-critical operations.
Security becomes business-aligned, not infrastructure-focused.
Governance, Accountability & Operational Discipline
Strong vulnerability management requires more than scanning tools.
We help establish executive oversight, defined remediation ownership, escalation pathways, change management integration, and audit-ready documentation. This embeds vulnerability management into your operational framework and ensures sustained risk reduction over time.
Security becomes structured and repeatable and not reactive and inconsistent.
Compliance & Regulatory Alignment
Strong vulnerability management requires more than scanning tools.
We help establish executive oversight, defined remediation ownership, escalation pathways, change management integration, and audit-ready documentation. This embeds vulnerability management into your operational framework and ensures sustained risk reduction over time.
Security becomes structured and repeatable and not reactive and inconsistent.
Our Vulnerability Management Process
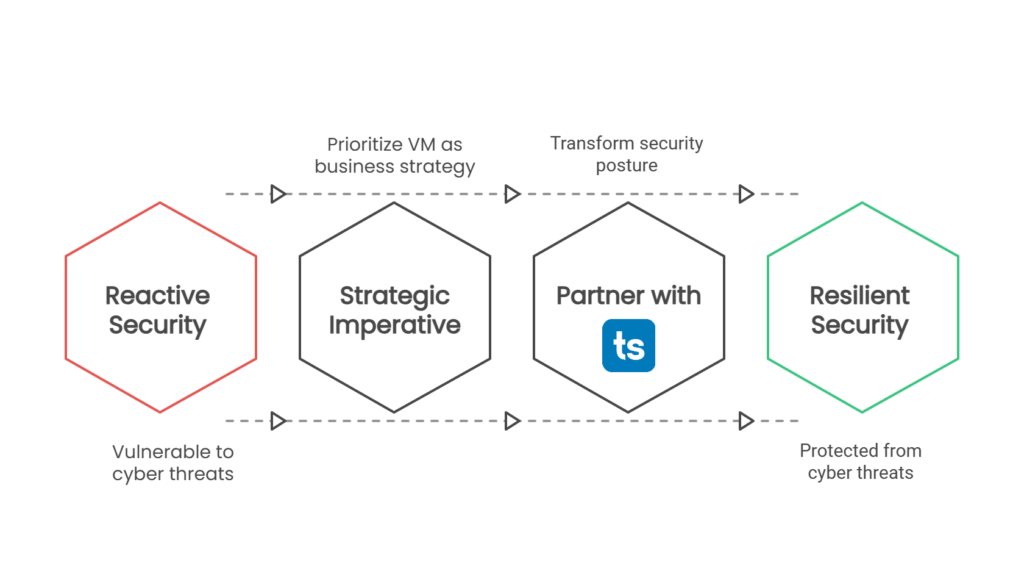
We follow a continuous, looped process that transforms vulnerability management from a reactive task into a strategic security capability.
By combining advanced automation with human expertise, we help organizations move from reacting to threats to building lasting cyber resilience.
Discover
Identify assets and exposures across your environment
Prioritize
Focus on real-world exploitability and business risk
Remediate
Execute structured and accountable fixes
Verify
Confirm exposure elimination
The Toos Solutions Difference
Many providers run scans and deliver reports.
Scanning Frequency
Continuous, 24/7 Monitoring
Prioritization
Risk-Based & Threat Intel Driven
Remediation Support
Coverage
Expertise
Dedicated Security Experts.
Why Vulnerability Management is Non-Negotiable
Cybersecurity is no longer a best practice, it is a core operational requirement. At the highest levels, including within the Canadian public sector, organizations are expected to take a structured, proactive approach to identifying and reducing cyber risk.
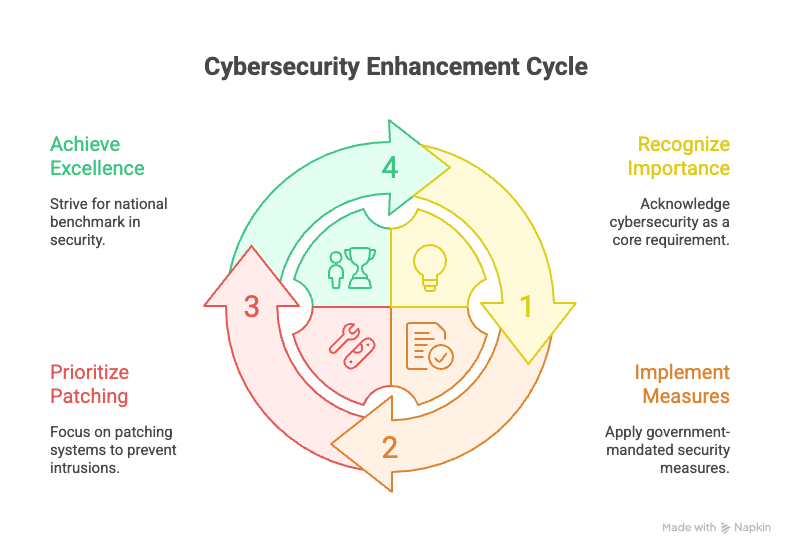
Our Approach: A Continuous Cycle of Cyber Resilience
Effective vulnerability management is not a one‑time fix or an annual check‑up, it is a continuous, strategic process that strengthens security over time. By consistently identifying, assessing, and reducing exposure, organizations can manage cyber risk as part of everyday operations rather than reacting after incidents occur.
Establish Executive-Level Command & Control:
We help you build the governance framework that embeds security into your culture, secures executive buy-in, and establishes clear lines of authority for rapid decision-making.
Achieve Complete Attack Surface Visibility
Focus Resources on What Matters Most
We move beyond raw vulnerability lists by applying a risk‑based prioritization model that focuses on issues with the greatest potential impact to your operations — maximizing efficiency and reducing wasted effort.
Decisive Risk‑Based Remediation
Align Technology to Business Impact
We maintain a comprehensive inventory of your IT assets and map them to critical business functions, ensuring vulnerability management efforts are aligned with your mission, services, and operational priorities.
Deliver Board-Ready Proof of Security
We translate technical findings into clear, measurable metrics that demonstrate risk reduction, track program effectiveness, and support audit, compliance, and board‑level reporting with confidence.
How We Protect Your Organization: A Deeper Look at Our Services
Effective cyber defense starts with clear visibility into your attack surface. Our approach ensures security efforts are aligned with what matters most to your organization.
We begin by establishing:
- A complete, up‑to‑date inventory of your technology environment
- Visibility across on‑premises servers, endpoints, cloud services, mobile devices, and operational technology
- Continuous awareness of new and changing assets
We then connect technology to business impact by:
- Mapping IT assets to critical business functions and services
- Identifying which systems support your mission‑critical operations
- Understanding the potential operational impact if specific assets are compromised
This business‑aligned approach allows us to:
- Prioritize security efforts based on real business risk
- Focus protection on the systems that matter most
- Allocate security resources efficiently and effectively
- Ensure vulnerability management decisions support organizational objectives
By grounding security decisions in business context, we enable smarter prioritization, clearer decision‑making, and stronger protection of your organization’s mission.
Proactive Vulnerability Identifitcation
This is the active “hunting” phase of our program, where we use a combination of advanced technologies and expert techniques to uncover security flaws before attackers can find and exploit them. We synthesize data from multiple sources to provide a comprehensive view of your security posture.








